Content
- Blockchain Overview
- Blockchain Consensus
- Blockchain Permissions
- Public Permissionless Blockchains
- Public Permissioned Blockchains
- Private Permissionless Blockchain
- Permissioned Blockchain
- Game Theory
- The Blockchain Trilemma
- Scalability
- Security
- Decentralisation
- The Layers of Blockchains
- Layer 1 Blockchains
- Layer 2 Blockchains
- Layer 0 Blockchains
- Conclusion
- DISCLAIMER
- FAQs
- What is a Blockchain and How Does it Work?
- What are the Different Types of Participants in a Blockchain Network?
- What are Consensus Algorithms in Blockchain?
- What is the Blockchain Trilemma?
- What are the Different Layers of Blockchains?
1 Feb, 23
The Fundamentals of Blockchain
- Blockchain Overview
- Blockchain Consensus
- Blockchain Permissions
- Public Permissionless Blockchains
- Public Permissioned Blockchains
- Private Permissionless Blockchain
- Permissioned Blockchain
- Game Theory
- The Blockchain Trilemma
- Scalability
- Security
- Decentralisation
- The Layers of Blockchains
- Layer 1 Blockchains
- Layer 2 Blockchains
- Layer 0 Blockchains
- Conclusion
- DISCLAIMER
- FAQs
- What is a Blockchain and How Does it Work?
- What are the Different Types of Participants in a Blockchain Network?
- What are Consensus Algorithms in Blockchain?
- What is the Blockchain Trilemma?
- What are the Different Layers of Blockchains?
Written by Finn Judell & Nathan Lenga
A blockchain is a distributed system that exists across a network of nodes within a peer-to-peer framework. Blockchain technology is founded on the principles of decentralisation and consensus that ensure trust within the network. These distributed platforms are fundamental to understanding the new financial system being built with cryptocurrencies and decentralised protocols.
The first real implementation of blockchain technology was used to create a digital peer-to-peer cash system, Bitcoin, in 2008; this marked the first solution to resolve the double-spending problem. The history of this revolutionary blockchain and its coin, BTC, is colourful and vague – we go into detail in this article. Since then, the technology has heralded a novel, decentralised platform, opening a multitude of use cases, such as decentralised finance (DeFi), non-fungible tokens (NFTs), and the execution of immutable, transparent smart contracts.
Blockchain Overview
Blockchain – referential to the name, is structurally a chain of ‘blocks’. Each ‘block’ represents a transaction or a bundle of transactions made by network participants. These blocks are chained together to create a database that acts as a permanent record of transactions. In the sake of Bitcoin, the transactions represent the transfer of digital currency from one entity to another. In other cases, such as on Ethereum, these transactions might represent the transfer of ownership of an NFT, or facilitate a lending agreement between one party to another. The chain of blocks is validated by a network of nodes (third-party computers) that work together to timestamp transactions and reach an agreement on the information outputted onto the blockchain.
There are two main types of participants within a blockchain network: users and validators. Users are individuals or entities that choose to use a blockchain to transact on the decentralised network as they choose. The other party, validators, play the role of protecting the network from becoming centralised, incentivised to append newly created blocks to the chain on a consistent basis. Both validators and users set up an account by generating a unique “public key” and “private key” on the blockchain, this is called a wallet.
Think of your public key as a username or email address. Your public key is available to the world; it is what individuals can use to send a transaction to your blockchain account. On the other hand, your private key represents a password; it is obfuscated from public eyes and used to access ownership of an on-chain wallet. An individual should never share their private key unless they intend for that party to have full access to their wallet. Often, private keys are hidden from the user and encrypted as a mnemonic phrase.
Blockchain Consensus
Blockchains rely on consensus algorithms for nodes to come to an agreement on the present state of a blockchain. This means that all nodes within the network need to come together at the same time and produce the same outcome or the same history of transactions. Consensus algorithms within blockchain networks solve a fundamental problem in cryptographic academia known as the Byzantine Generals Problem. This issue emphasises the difficulty in ensuring that decentralised parties reach a consensus without relying on a centralised, trusted entity.
Consensus algorithms are an integral part of blockchain infrastructure because they ensure that every new block added to a chain is the one and only version of the truth that is agreed upon by the majority of nodes on the blockchain. Notably, this truth, which is emblematic of the history of transactions on the blockchain, is determined in a decentralised manner, as opposed to leveraging a server. Effective consensus algorithms can establish a common agreement between unknown nodes within the network.
The Proof of Work (PoW) consensus algorithm was created by Satoshi Nakamoto, an anonymous individual or group behind the creation of Bitcoin. The PoW algorithm’s job is to determine a node (known as a ‘miner’ in the context of PoW) to execute the next block. Miners are selected by competing against each other in a race to guess a specific hash through the use of a hash function known as SHA-256. These functions have a deterministic output for every input; therefore, though the output of the hash function might seem random, for each unique input, there will be a unique output. Miners use computing power to randomly guess this hash; the first computer to correctly generate the correct hash is rewarded with the blockchain’s native cryptocurrency – thus incentivising miners to act in the best interest of the network. The most commonly cited criticism of Proof of Work is its impact on the planet, with Bitcoin alone reportedly making up 0.1% of the world’s greenhouse gas emissions. However, some would argue that Bitcoin’s energy consumption is a feature, not a bug as miners prove they have capital at risk by expending energy.
Proof of Stake (PoS) is the most common alternative to PoW – recently being adopted by Ethereum, the second largest blockchain network by transaction volume and market capitalisation. The protocol was originally proposed by entities going under the pseudonyms Sunny King and Scott Nadal in their paper entitled “PPCoin: Peer-to-Peer Crypto-Currency with Proof-of-Stake”. Instead of using energy expenditure as a form of financial collateralisation like PoW, PoS requires nodes to stake direct financial capital to secure the network. This financial capital is generally in the form of the blockchain protocol’s native asset. The staked assets can be burnt (destroyed) if the validator behaves maliciously or performs lazily.
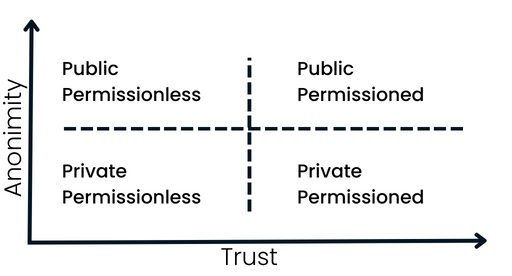
Blockchain Permissions
Public blockchains are transparent and open to use, whereas private blockchains are not open to use from non-authorised parties. Permissionless blockchains allow anyone to participate in validating the network, whereas permissioned blockchains cannot be validated by non-authorised parties. Different use cases may require different types of protocol permissions, resulting in several unique structures to accommodate the needs of alternating companies. In the wider crypto industry that strives to bring financial transparency and instruments to all, public and permissionless blockchains have dominated the market.
Public Permissionless Blockchains
Public permissionless blockchains, such as Bitcoin and Ethereum, are open for anyone to join and participate in the network. There are no restrictions on who can validate transactions, add new blocks to the chain, or access the transaction data. These networks are decentralised and operate on a consensus mechanism, such as PoW or PoS, which allows for trustless and peer-to-peer transactions without the need for a central authority. However, public permissionless blockchains lack privacy and regulatory oversight.
Public Permissioned Blockchains
Public permissioned blockchains, on the other hand, are open for anyone to join but have certain permissions in place for certain network activities. A central authority or consortium of authorities can control the network and set permissions for different types of participants. This approach allows for increased regulatory oversight, but it also means that the network is not truly decentralised. Public permissioned blockchains are typically used in scenarios where the need for regulatory compliance, transparency, and security is high, such as in financial services and supply chain management.
Private Permissionless Blockchain
Private permissionless blockchains, also known as consortium blockchains, are similar to public permissionless blockchains, but the network is restricted to a certain group of pre-approved participants. These participants can validate transactions, add new blocks to the chain, or access the transaction data. Private permissionless blockchains can be used in scenarios where a group of organisations want to share data and collaborate on a specific project, but do not want to make the data public.
Permissioned Blockchain
Private permissioned blockchains, also known as fully private blockchains, are restricted to a specific group of pre-approved participants and have certain permissions in place for certain network activities. The network is controlled by a central authority and only authorised participants can validate transactions, add new blocks to the chain, or access the transaction data. Private permissioned blockchains can be used in scenarios where data needs to be kept highly confidential, such as in government and military operations, or in scenarios where regulatory compliance is a must.
Game Theory
Game theory is the study of strategic decision-making. Within a blockchain environment, game theory is implemented to ensure that all actors within the network are appropriately incentivised to act in the best interests of the blockchain, while disincentivizing self-interest and malicious activity. When combining these attempts, blockchains encourage their participants to coordinate and consequently achieve a collective goal of protecting the network holistically.
Blockchain game theory principles imply that if everyone works dishonestly, nobody can receive any token rewards. Simultaneously, if everyone works honestly, everyone gets an equal chance at obtaining a reward. If some parties decide to work honestly and others maliciously, then the latter’s reward drops to zero and those tokens are allocated towards the former’s reward. For PoW, miners satisfy exorbitant costs for the energy they use when competing against others. These fees represent miners’ collateral that they are at risk of losing if they cease acting as honest parties; this is the primary disincentive that discourages malicious behaviour from network participants. In PoS, validators stake financial collateral to incentivise validators to work honestly. Rewards can be distributed differently depending on the type of PoS model; some frameworks prioritise validators with the most cryptocurrency staked.
Blockchains like Bitcoin and Ethereum have successfully implemented game theory within a public and permissionless environment. Incentivising users to act within the best interest of the network by rewarding validators with the blockchain’s native currency has proven highly effective in ensuring the longevity of the chain. All blockchains are susceptible to a 51% attack, implying that an entity can gain full control over a blockchain network if it can manipulate the majority of the total collateral within the network. The sheer volume of validators that are present within popular blockchains makes it considerably expensive to achieve a 51% attack.
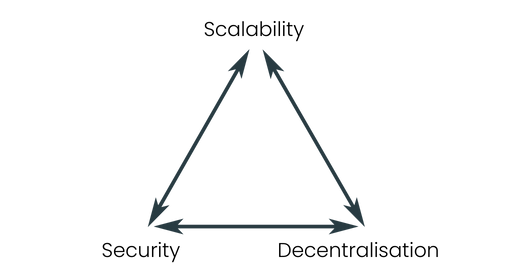
The Blockchain Trilemma
While blockchains have indented a significant impact on the world, the technology comes with various limitations that require attention from any party looking to leverage this distributed network. The blockchain trilemma, coined by Vitalik Buterin, the co-founder of Ethereum, highlights the limitations of blockchain technology and explains the various trade-offs that are made within the infrastructure. The blockchain trilemma consists of three fundamental benefits of blockchain systems.
The blockchain trilemma implies that only two of three benefits at any given time can be successfully implemented. Consequently, any priority of the three benefits will result in a reduction of one or both of the benefits within the trilemma. It’s important to note that the blockchain trilemma is just a model to conceptualise the limitations of blockchain technology. There is no inherent law stating that all three benefits of blockchain cannot be obtained collectively.
Scalability
Depending on the way a blockchain is configured and the transaction volume requested by users of a chain, a blockchain may experience latency in transaction speed and its ability to append data to the chain. Given the rapid adoption of blockchain technology, scalability has been a prioritised concern. Truly scalable infrastructure is extremely important for a plethora of blockchain use cases.
Security
A blockchain system should be able to defend itself from an attack. A blockchain will generally implement security using financial incentives that originate in game theory, ensuring that it is more expensive to exploit the blockchain than the total value earned through the exploitation itself. The most secure chains will not be susceptive to reorganisation attacks, whereby the blocks are reorganised by a party or several parties. Further, security entails that a blockchain is not vulnerable to network-specific attacks, such as a denial of service or distributed denial of service exploit.
Decentralisation
Decentralisation is the term used to describe a system that distributes control over an array of decision-makers and parties, rather than being controlled by one single, centralised authority. Within a blockchain setting, decentralisation is used to ensure that transactions added to blocks and eventually appended to the chain have been verified by a multitude of parties. In this sense, servers are not used to cross-reference transactions. Many variables contribute to the decentralisation of a blockchain; architectural decentralisation, referring to the number of nodes participating in the network, political decentralisation, which is based on how many entities control the chain’s nodes, and logical decentralisation, relating to the interface(s) for a blockchain and its data structures.
The Layers of Blockchains
Originally, there was only a single layer of blockchains. This layer executed transactions, assisted nodes coordinate to reach consensus and support the functionality of smart contracts. Over time, more layers have emerged to introduce new features that are needed to scale blockchains and onboard new users.
Layer 1 Blockchains
As explained, layer 1s were the first layer of blockchains launched, beginning with the Bitcoin network. Layer 1s are the most dominant infrastructure layer within the cryptocurrency ecosystem, seeing the most adoption and monetary value locked into them. After the launch of Ethereum, most layer 1 blockchains have offered smart contracts, resulting in numerous applications being created on top of the chain. Layer 1s are significant given that they enable more diverse and unique decentralised applications to launch without the requirement of building their own blockchain.
This layer of the blockchain stack can be analogised to a city; the city is governed by its populace and allows businesses to emerge, generating profits and adoption of the city. Within this city, there are roads to support traffic when citizens want to move around and make the most of what their city has to offer; in the blockchain context, transactions are equivalent to traffic. However, as the city’s population grows, the roads become insufficient to accommodate the exponentially increasing traffic. So as not to prevent the growth of the city, its population decides to build more efficient travel infrastructure, including trains, trams, ferries and more, for its citizens – this infrastructure is what layer 2s represent.
Layer 2 Blockchains
Symbolising the revolutionary technology that allows citizens of the city (layer 1s) to commute efficiently, layer 2s fundamentally have the purpose of easing congestion of transactions on layer 1s like Ethereum. Upon this realisation that demand for the blockchain would eventually eclipse its supply, layer 2s emerged to increase layer 1s’ ability to scale. Also known as rollups, layer 2s facilitate thousands of transactions, compressing them into a smaller number of transactions before posting them on the layer 1. This ensures that whilst the scalability and efficiency of layer 2s are obtained, the security and decentralisation of layer 1s are nonetheless leveraged. Though transactors on layer 2s still need to pay gas fees, these costs are distributed between all users, rendering these networks significantly more usable for a broader audience when compared to layer 1s.
Ultimately, however, rollups derive their utility from layer 1s – without a city that has a sufficiently large population, the efficient travel infrastructure is unnecessary as congestion of roads is not a threat. As more entities are onboarded into the blockchain space, more cities will be needed; similarly to how cities are created in various geographical areas based on demand, novel layer 1s are needed to respond to different inefficiencies in the market. Notably, establishing a layer 1 blockchain, like erecting a new city, is arduous and expensive. To mitigate this difficulty and cost, countries are required to fund the building of cities and provide the infrastructure they have already designed; these countries represent layer 0s.
Layer 0 Blockchains
Although not all layer 1 blockchains exist upon layer 0s, these networks have been gaining meaningful traction recently due to their ability to offer developers software development kits (SDKs) that assist them in building layer 1s. As the infrastructure underpinning layer 1 blockchains, layer 0s ensure that all blockchains are natively connecting, consequently establishing communication lines between autonomous chains. This layer significantly reduces the technical and fiscal requirements of building novel layer 1s. Resultantly, more blockchains are being built to accommodate specific needs such as gaming-focused and DeFi-focused chains.
Layer 0s serve the role of a country that is looking to stimulate population growth through the modernization of cities. These countries have the funding, experience and infrastructure to expedite the creation process of new, diverse and unique cities, bringing individuals into the population at an order of magnitude previously thought to be impossible. This is what layer 0s offer for the cryptocurrency industry; a platform to efficiently establish layer 1 blockchains that can be optimised to respond to a distinct set of needs.
Conclusion
Blockchains are a useful tool to establish cryptographic, decentralised trust within systems. Use cases for blockchain technology continue to emerge and evolve as more innovative technology is created. With that said, various limitations apply to blockchains. To combat these limitations, developers have taken a “not one size fits all” approach, developing a number of different blockchains designed for particular use cases. Additionally, blockchain developers may opt to work with modular solutions, creating application-specific blockchains that cater to different areas of blockchain technology while letting other blockchains handle specific functions within the same development stack.
DISCLAIMER
Zerocap Pty Ltd carries out regulated and unregulated activities.
Spot crypto-asset services and products offered by Zerocap are not regulated by ASIC. Zerocap Pty Ltd is registered with AUSTRAC as a DCE (digital currency exchange) service provider (DCE100635539-001).
Regulated services and products include structured products (derivatives) and funds (managed investment schemes) are available to Wholesale Clients only as per Sections 761GA and 708(10) of the Corporations Act 2001 (Cth) (Sophisticated/Wholesale Client). To serve these products, Zerocap Pty Ltd is a Corporate Authorised Representative (CAR: 001289130) of AFSL 340799
All material in this website is intended for illustrative purposes and general information only. It does not constitute financial advice nor does it take into account your investment objectives, financial situation or particular needs. You should consider the information in light of your objectives, financial situation and needs before making any decision about whether to acquire or dispose of any digital asset. Investments in digital assets can be risky and you may lose your investment. Past performance is no indication of future performance.
FAQs
What is a Blockchain and How Does it Work?
A blockchain is a distributed system that operates across a network of nodes within a peer-to-peer framework. It’s based on principles of decentralisation and consensus, ensuring trust within the network. Each ‘block’ in the blockchain represents a transaction or a bundle of transactions made by network participants. These blocks are chained together to create a database that acts as a permanent record of transactions.
What are the Different Types of Participants in a Blockchain Network?
There are two main types of participants within a blockchain network: users and validators. Users are individuals or entities that use a blockchain to transact on the decentralised network. Validators, on the other hand, protect the network from becoming centralised and are incentivised to append newly created blocks to the chain consistently.
What are Consensus Algorithms in Blockchain?
Consensus algorithms are used for nodes to agree on the present state of a blockchain. They solve a fundamental problem known as the Byzantine Generals Problem, which emphasises the difficulty in ensuring that decentralised parties reach a consensus without relying on a centralised, trusted entity. Examples of consensus algorithms include Proof of Work (PoW) and Proof of Stake (PoS).
What is the Blockchain Trilemma?
The blockchain trilemma, coined by Vitalik Buterin, the co-founder of Ethereum, highlights the limitations of blockchain technology. It suggests that only two of the three benefits – scalability, security, and decentralisation – can be successfully implemented at any given time.
What are the Different Layers of Blockchains?
Blockchains can have multiple layers. Layer 1 blockchains, like Bitcoin and Ethereum, execute transactions and support the functionality of smart contracts. Layer 2 blockchains, also known as rollups, increase the scalability of Layer 1s by facilitating thousands of transactions and compressing them into a smaller number of transactions before posting them on the Layer 1. Layer 0 blockchains underpin Layer 1 blockchains and ensure that all blockchains are natively connecting, establishing communication lines between autonomous chains.
Like this article? Share
Latest Insights
Weekly Crypto Market Wrap: 11 May 2026
Zerocap is a market-leading digital asset firm, providing trading, liquidity and custody to forward-thinking institutions and investors globally. To learn more, contact the team at
Weekly Crypto Market Wrap: 4 May 2026
Zerocap is a market-leading digital asset firm, providing trading, liquidity and custody to forward-thinking institutions and investors globally. To learn more, contact the team at
Weekly Crypto Market Wrap: 27 April 2026
Zerocap is a market-leading digital asset firm, providing trading, liquidity and custody to forward-thinking institutions and investors globally. To learn more, contact the team at
Receive Our Insights
Subscribe to receive our publications in newsletter format — the best way to stay informed about crypto asset market trends and topics.



 Share
Share  Tweet
Tweet  Post
Post 